 Apple's engineers deleted almost all the console utilities from iOS, but in case of installing of OpenSSH on a hacked iPhone you also need to install a package with BSD-environment. Now meet the old friends - curl, scp, zsh, tar, bzip2 aaaaand, guess who? - gunzip!
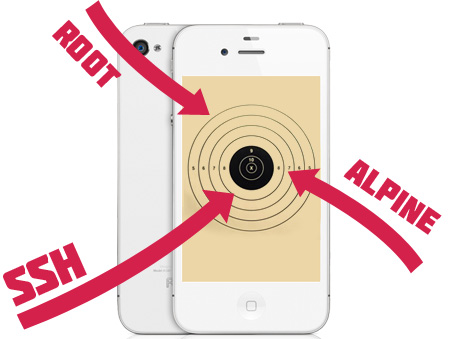
Like in any other Unix-based system iOS has superuser under name root and standard password - alpine. Six letter in lowercase - a very bad idea for root password. But don't be afraid until your iPhone is not hacked (jailbroken) because until it's clean there's no place to enter this login and password. So it's better for you to check your root password to any other you'd like. Once you're protected, let's start the fun!
For detecting your potential victim you need to be connected to Wi-Fi. Now we need to run a nmap scan. Just run scanning as usual, for instance:
nmap -O 10.0.0.*
and you'll see such data among other hosts:
Not shown: 1714 closed ports
PORT STATE SERVICE
22/tcp open ssh
MAC Address: XX:XX:XX:XX:XX:XX (Apple)
Device type: phone|media device
Running: Apple embedded
OS details: Apple iPhone mobile phone or iPod Touch audio player (Darwin 9.0.0d1)
Apple's engineers deleted almost all the console utilities from iOS, but in case of installing of OpenSSH on a hacked iPhone you also need to install a package with BSD-environment. Now meet the old friends - curl, scp, zsh, tar, bzip2 aaaaand, guess who? - gunzip!
Like in any other Unix-based system iOS has superuser under name root and standard password - alpine. Six letter in lowercase - a very bad idea for root password. But don't be afraid until your iPhone is not hacked (jailbroken) because until it's clean there's no place to enter this login and password. So it's better for you to check your root password to any other you'd like. Once you're protected, let's start the fun!
For detecting your potential victim you need to be connected to Wi-Fi. Now we need to run a nmap scan. Just run scanning as usual, for instance:
nmap -O 10.0.0.*
and you'll see such data among other hosts:
Not shown: 1714 closed ports
PORT STATE SERVICE
22/tcp open ssh
MAC Address: XX:XX:XX:XX:XX:XX (Apple)
Device type: phone|media device
Running: Apple embedded
OS details: Apple iPhone mobile phone or iPod Touch audio player (Darwin 9.0.0d1)
 Sure, the scanning process with -O key is very long and boring process, so there's a little automation cheat. Hacked iPhone runs not only sshd but mDNSResponder (Zeroconf by Apple) as well. That means that device tells everyone about the services offers on startup. So you just have to run SFTP-client with Bonjour support, and he'll let you know when the new host appears online.
Now you know how to hack someone's iPhone and search for useful data, but how does it look like? They can be stored as is, in .plist files or SQLite bases. How to get them? Read the second part of Funny and Useful iPhone Hacks.
Sure, the scanning process with -O key is very long and boring process, so there's a little automation cheat. Hacked iPhone runs not only sshd but mDNSResponder (Zeroconf by Apple) as well. That means that device tells everyone about the services offers on startup. So you just have to run SFTP-client with Bonjour support, and he'll let you know when the new host appears online.
Now you know how to hack someone's iPhone and search for useful data, but how does it look like? They can be stored as is, in .plist files or SQLite bases. How to get them? Read the second part of Funny and Useful iPhone Hacks. Recent Blog

Ultimate Guide: How to turn Off Restricted Mode on iPhone?

Automate Apple GSX check result obtaining?

iRemove Unlock iPhone 5S, 5C, 5, SE, 4S/4 Software

MacOS High Sierra Features: Set Up Websites in Safari on Mac
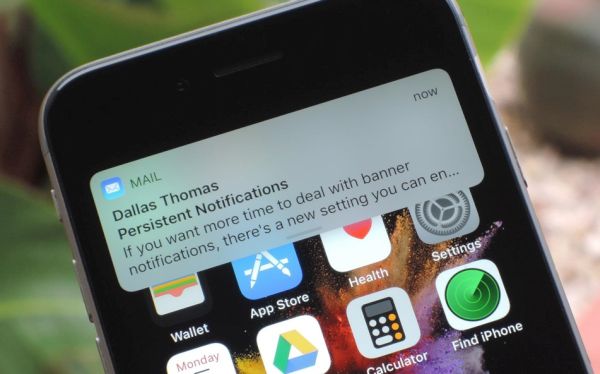
How to Enable iOS 11 Mail Reply Notification on iPhone 7

How to Bypass Apple Watch Passcode Problem
LetsUnlock Services List
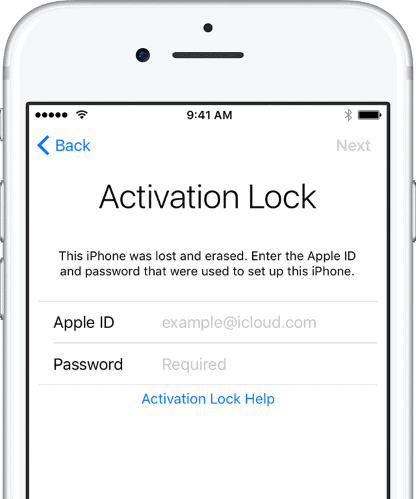
iPhone & iPad Activation Lock Bypass
Use LetsUnlock iCloud Tool to bypass Activation Lock Screen on iPhone and iPad running on iOS version up to 14.6.
Read More
Unlock Passcode Disabled iPhone or iPad
LetsUnlock iCloud Tool is ready to remove Find My and unlock your passcode disable device running on iOS 13.x.x in one click!
Read More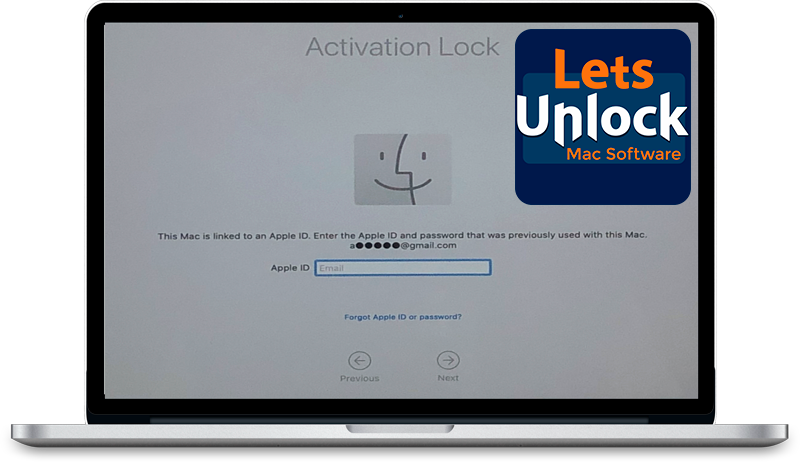
MacOS iCloud Activation Lock Bypass
The LetsUnlock Mac iCloud Activation Lock Bypass Tool will help you to remove Activation Lock on an iCloud locked Mac which is stuck on Activation Lock Screen with no need to enter the correct Apple ID and password.
Read More
Mac EFI Firmware Passcode Bypass
The LetsUnlock EFI Bypass Tool is a one button solution, which you click to start the EFI Unlock process. Bypass EFI with out password! Everything else does the software.
Read More
MacOS iCloud System PIN Bypass
The LetsUnlock MacOS iCloud System PIN Bypass Tool was designed to bypass iCloud PIN lock on macOS without passcode!
Read More