 Combined Database and IMEI Number Bans
There is a report on CNET that shares details about T-Mobil and AT&T blocked iPhone databases merging. It is already working, at least it is alive by now. Both mobile operators can block gadgets from being used on their networks. You might have guessed that they simply ban iOS IMEI number which is unique for every Apple smartphone.
IMEI number identifies the iDevices and it carries important information about iPhone owner and the network he or she is using. Once the IMEI number is blocked, its device’s holder will not be able to make phone calls on domestic networks.
Fewer Thefts from Now On?
Even if your iPhone is stolen but its IMEI number is banned the thief won’t be able to make calls because no SIM cards will work on this device.
Nowadays only two carriers, AT&T and T-Mobile, will use this base and stop iDevices from being used by non-owners. Other mobile operators [Verizon and Sprint] will support this initiative and merge their databases by fall 2013.
Do you believe that this plan can really help iPhone customers? Personally I think it is a great idea however it will not help to find your handset in case it has really been stolen. It will save your phone bills which is cool and maybe “dry up the aftermarket for stolen devices,” according to Steve Largent from CTIA.
Combined Database and IMEI Number Bans
There is a report on CNET that shares details about T-Mobil and AT&T blocked iPhone databases merging. It is already working, at least it is alive by now. Both mobile operators can block gadgets from being used on their networks. You might have guessed that they simply ban iOS IMEI number which is unique for every Apple smartphone.
IMEI number identifies the iDevices and it carries important information about iPhone owner and the network he or she is using. Once the IMEI number is blocked, its device’s holder will not be able to make phone calls on domestic networks.
Fewer Thefts from Now On?
Even if your iPhone is stolen but its IMEI number is banned the thief won’t be able to make calls because no SIM cards will work on this device.
Nowadays only two carriers, AT&T and T-Mobile, will use this base and stop iDevices from being used by non-owners. Other mobile operators [Verizon and Sprint] will support this initiative and merge their databases by fall 2013.
Do you believe that this plan can really help iPhone customers? Personally I think it is a great idea however it will not help to find your handset in case it has really been stolen. It will save your phone bills which is cool and maybe “dry up the aftermarket for stolen devices,” according to Steve Largent from CTIA. Recent Blog

Ultimate Guide: How to turn Off Restricted Mode on iPhone?

Automate Apple GSX check result obtaining?

iRemove Unlock iPhone 5S, 5C, 5, SE, 4S/4 Software

MacOS High Sierra Features: Set Up Websites in Safari on Mac
How to Enable iOS 11 Mail Reply Notification on iPhone 7

How to Bypass Apple Watch Passcode Problem
LetsUnlock Services List
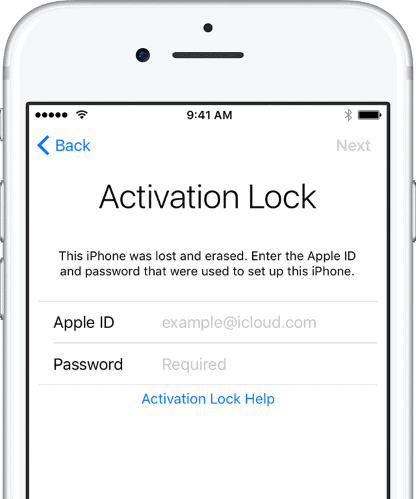
iPhone & iPad Activation Lock Bypass
Use LetsUnlock iCloud Tool to bypass Activation Lock Screen on iPhone and iPad running on iOS version up to 14.6.
Read More
Unlock Passcode Disabled iPhone or iPad
LetsUnlock iCloud Tool is ready to remove Find My and unlock your passcode disable device running on iOS 13.x.x in one click!
Read More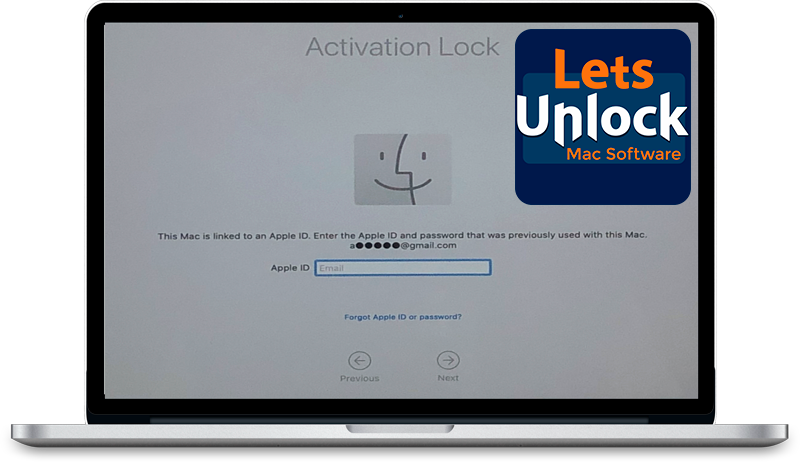
MacOS iCloud Activation Lock Bypass
The LetsUnlock Mac iCloud Activation Lock Bypass Tool will help you to remove Activation Lock on an iCloud locked Mac which is stuck on Activation Lock Screen with no need to enter the correct Apple ID and password.
Read More
Mac EFI Firmware Passcode Bypass
The LetsUnlock EFI Bypass Tool is a one button solution, which you click to start the EFI Unlock process. Bypass EFI with out password! Everything else does the software.
Read More
MacOS iCloud System PIN Bypass
The LetsUnlock MacOS iCloud System PIN Bypass Tool was designed to bypass iCloud PIN lock on macOS without passcode!
Read More